Although container-related technology existed before 2013, Docker revolutionized and propelled it into the mainstream. Using Docker, developers could automatically create containers from application source code, share libraries, and reuse containers.
Docker enables you to track container image versions, roll back to an earlier iteration, and track who built a specific one. You can even upload only the deltas between two versions.
Ultimately, Docker containers do not need modification to run across any desktop, cloud environment, or data center. They just work.
However, on December 2, 2020, Kubernetes contributors announced that they would deprecate the Docker runtime starting with version 1.20. In Docker’s place, Kubernetes would use the Container Runtime Interface (CRI), which supports a broader range of runtimes compared to Docker.
But what exactly is Docker, and what Docker alternatives do you have available to you today?
What Is Docker?
Docker is an open platform for container development, deployment, and management. It enables developers to separate their applications from the underlying infrastructure. This reduces the time between coding and deploying to production, making the development process more effective.
The Docker platform offers tools for handling container lifecycles. With Docker, applications and their components can be developed inside containers. Containers are used as the primary means of distributing and testing software. When ready, you can deploy these containers into production environments.
Docker is also beneficial for CI/CD processes. Developers can write code locally and distribute their projects through Docker containers. These containers undergo automated and manual testing in test environments. If any errors are detected, they can be corrected during the development stage and then rolled out again for further testing.
Research Report
FinOps In The AI Era: A Critical Recalibration
What 475 executives told us about AI and cloud efficiency.
Is Docker Still Relevant In 2026
Docker remains relevant to most container projects, applications, and developers today thanks to its modern tools, compatibility, large community, and ease of use. That said, teams evaluating a docker replacement often cite licensing changes, Kubernetes deprecation of Docker’s runtime, or the need for daemonless workflows as their primary reasons for switching. It remains widely used for container development and deployment workflows.
However, several factors are driving interest in Docker alternatives. For one, some developers want to avoid running the Docker daemon entirely — especially in secure or restricted environments where rootless or daemonless tools are preferred. Others want to use the same container technology consistently across development and production, which isn’t always seamless with Docker.
Additionally, the rise of Kubernetes-native tools and the deprecation of the Docker runtime in Kubernetes have encouraged teams to explore OCI-compliant alternatives. Licensing changes to Docker Desktop and uncertainty surrounding the direction of Docker Inc. have also prompted teams to re-evaluate their dependencies.
If you’re concerned about Docker’s long-term fit in your stack, there are plenty of capable alternatives to consider.
Can You Use Containers Without Docker?
Using containers without Docker is possible. At times, it’s even more favorable, depending on your project’s needs and limitations. While Docker is one of the most popular container management and deployment platforms, it is not the only option.
Other alternatives offer the features and integrations that ensure containerization retains its flexibility and usefulness.
What Are The Best Docker Alternatives In 2026?
Docker has several standalone alternatives, some of which offer virtualization technologies and cross-platform support. There are also Open Container Initiative (OCI) tools that work with Docker, replace some Docker components, or work with other Docker alternatives to form robust Docker competitors.
Note: You won’t find Kubernetes here. Despite popular comparisons, Kubernetes is not a direct alternative to Docker; that would be Docker Swarm, Docker’s own container orchestration tool.
Here is a quick summary table for the top alternatives:
|
Tool |
Best for |
Why use it |
|
Podman |
Daemonless container workflows |
Script-friendly, no daemon, integrates with Podman |
|
Buildah |
Building OCI images without Docker |
Script-friendly, no daemon, integrates with Podman |
|
Containerd |
Lightweight container runtime |
Production-grade, used by Docker and Kubernetes |
|
RunC |
Low-level OCI runtime |
Tiny footprint, direct Linux container execution |
|
LXD |
System containers and VMs |
Advanced Linux virtualization with snapshots, clustering |
|
Vagrant |
Replicable virtual dev environments |
Complete VM lifecycle management, great for testing across platforms |
|
Kaniko |
Building containers in Kubernetes |
No Docker daemon needed, rootless builds |
|
ZeroVM |
Single-process sandboxing |
Lightweight, fast startup, app-level isolation |
1. Buildah – Command-line tool for OCI images and containers
If you want to build OCI container images without installing a standalone container runtime or daemon, Buildah may be your best choice. Creating OCI images is Buildah’s primary focus. Its commands replicate the commands in a Dockerfile. The result is that you can create images with or without Dockerfiles without needing root privileges. The images will still work with both Docker and Kubernetes.
Buildah aims to deliver a lower-level coreutils interface for building images. By not requiring Dockerfiles, you can also integrate different scripting languages into your build process. It also uses a lightweight fork-exec model rather than running as a daemon. It is also implementable with other tools, like Podman, Skopeo, and Dive.
2. LXD – Linux daemon by Ubuntu
Linux Daemon (LXD) manages virtual machines and system containers on Linux systems. It is image-based, fast, secure, and highly scalable. You can set it up in a cluster management environment to manage even more complex workloads through VMs, containers, or both within a set of machines.
LXD can be described as a REST API that connects to the Linux Containers (LXC) library, libxlc. However, it has several powerful advantages over LXC. These include direct hardware access, which reduces operational costs while increasing efficiency and density. It also offers advanced snapshot features such as automatic expiry and scheduling.
3. Vagrant – CL utility for VMs lifecycle management
With HashiCorp’s Vagrant, you can replicate multiple conditioned virtual environments across a variety of operating systems and virtual machines. It helps set up a virtual environment that you can replicate multiple times on different networks, VMs, and OSs. This facilitates interoperability. You can also create matching virtual environments to stage, develop, and deploy apps.
Vagrant also enables you to create and share VM images on different platforms, helping you set up virtual environments that share libraries and compilers. Conversely, Docker frequently reverts to the old image after restarting. Moreover, unlike Docker, which provides user-level isolation, Vagrant allows you to use different tools and capabilities together.
Vagrant works with most virtualization software, including VMware and VirtualBox.
4. Containerd – A simple yet robust container runtime
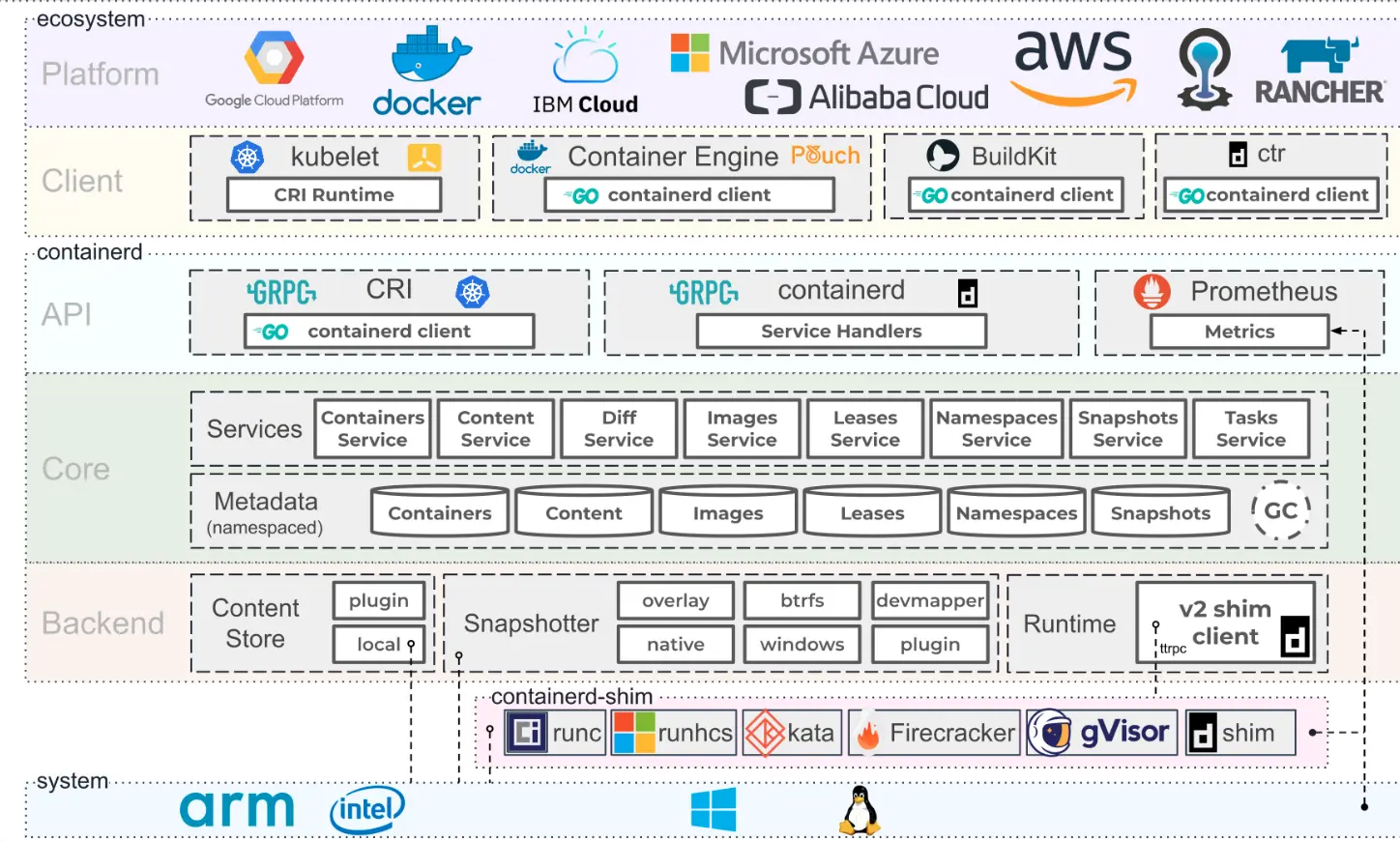
Containerd is a CNCF-graduated container runtime project that has been Docker’s preferred container runtime for years. Docker currently uses runC. Containerd handles all aspects of container lifecycle management for its host system. It creates, runs, and destroys containers as needed. It also handles image transfers and storage, container supervision, and low-level storage and network attachments. Teams running Kubernetes on AWS often default to Containerd after migrating off Docker.
Containerd is also suitable for multi-tenant operations when combined with CAS storage (for global images). Another advantage is that it integrates with numerous tools and services, including runC, Kubernetes Engine, Amazon Kubernetes Service (AKS), and Azure Kubernetes Service (AKS). Containerd is also available as a daemon for Windows. For teams building Docker alternatives for Kubernetes, Containerd is often the first stop — it’s the default runtime in most managed Kubernetes services including EKS, GKE, and AKS.
5. ZeroVM – Open-source virtualization with sandbox support

ZeroVM is a portable, lightweight, and secure tool for creating an isolated environment for running single processes at a time. This approach is based on the Chromium Native Client (NaCl) project. In contrast, other virtualization and container technologies provide a fully virtualized OS and running environment for executing multiple processes.
Instead, ZeroVM embeds an application in an isolated environment to enable virtualization at the app level, without requiring an operating system or kernel. This setup boosts deployment speed (startup in under six milliseconds) and improves security for processes or apps that run unverified code across different virtual environments.
6. Podman – Open-source, daemonless container engine for Linux
Podman is a Linux-native container engine that utilizes the libpod library for managing container lifecycle tools. The program excels at executing the commands and tasks that update and tweak OCI images, including pulling and tagging. It also helps create, run, and maintain the containers you create from those images. While it runs containers on Linux, you can still use Podman to run them on Windows and Mac systems with a Podman-managed virtual machine.
Note that Buildah and Podman have different concepts of a container. While Podman allows you to create more long-lived containers, Buildah containers enable you to add content back to a container image. Think of this way: the buildah run command imitates the RUN command in a Dockerfile, while the podman run command mimics the docker run command. This, along with their underlying storage system differences, prevents you from seeing Buildah containers within Podman, and vice versa.
7. BuildKit – Image building engine for Docker
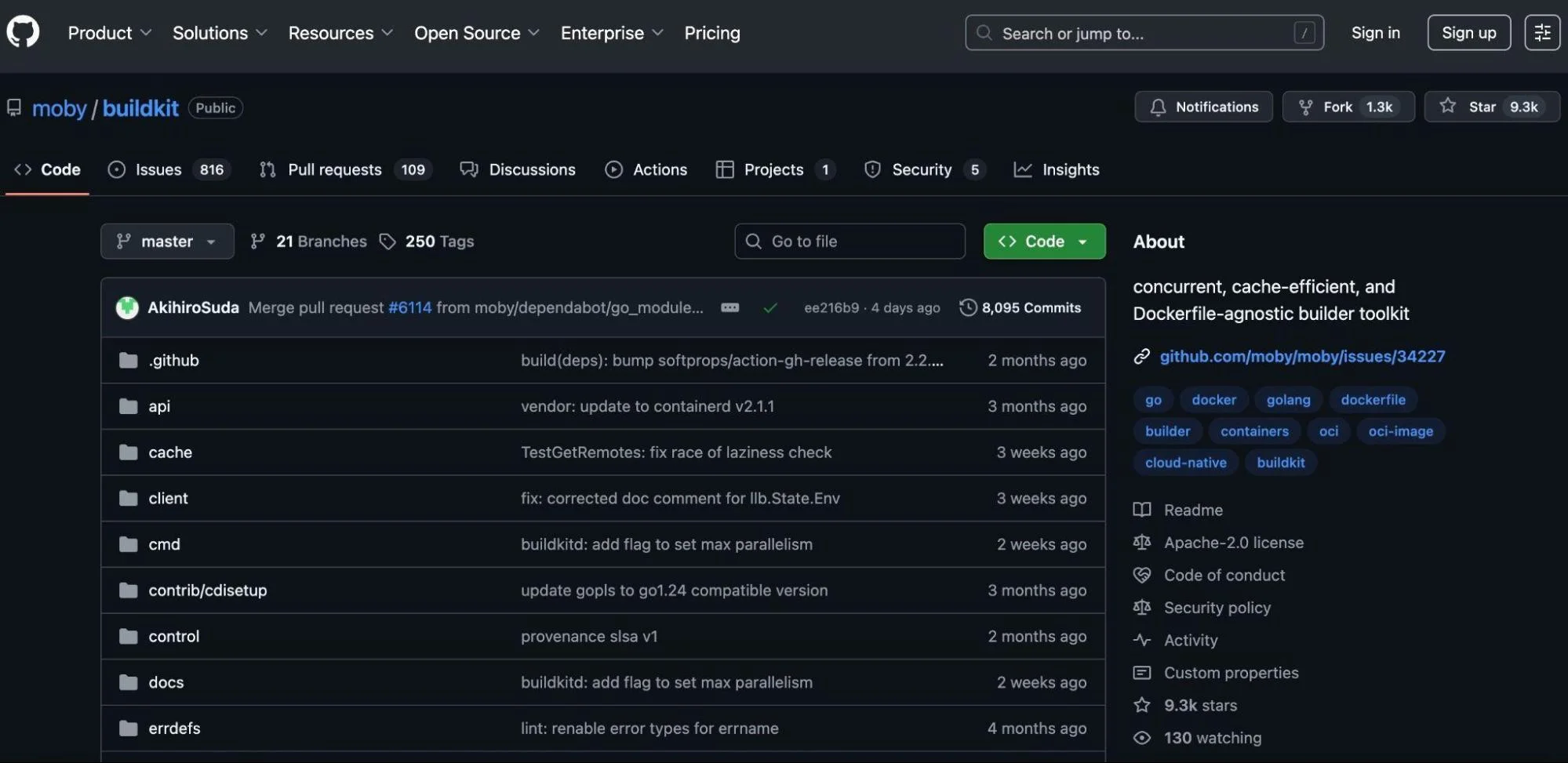
BuildKit is an image-building engine from the Moby Project. It is available as part of Docker Build (Docker version 18.09 and later) and as a standalone tool under Moby.
Like Docker, BuildKit runs on a daemon. However, while Docker builds each image layer at a time, BuildKit leverages parallel build processing to improve performance in faster builds.
Its enhanced caching also ensures that you do not have to rebuild each layer continually.
BuildKit also supports skipping unused stages, rootless builds, and facilitates incremental builds. Additionally, it provides an enhanced plugging architecture to improve extensibility. This is how some developers are able to use BuildKit to convert functions into containers or to complete CI pipelines.
8. RunC – OCI-compliant container runtime tool
RunC is a GitHub-hosted, Command-Line Tool built with Go (v1.17 or later) for spawning and running containers on Linux systems. It does this based on OCI specifications. RunC used to be a low-level tool, meaning using it directly as an end user wasn’t advisable. A standalone version is now available, allowing you to use runC either as part of Docker or separately.
It is independent of Docker and serves as a lightweight, universal, and portable container runtime — similar to Containerd, but without support for Windows.
9. Firecracker – Lightweight virtualization for serverless and secure containers
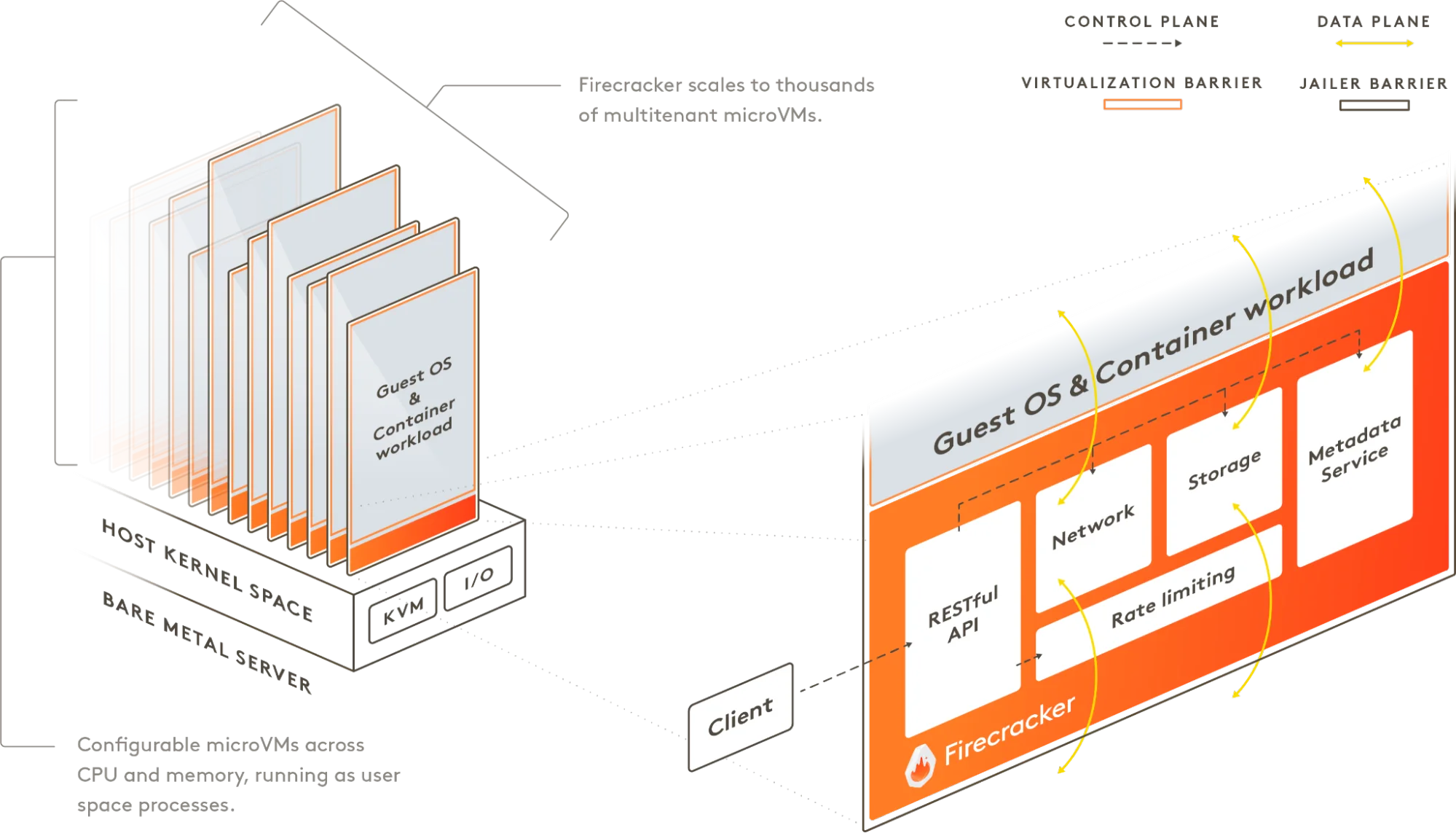
Firecracker is a virtualization tool from AWS. It runs microVMs, tiny virtual machines built for speed and isolation. While it was designed to power AWS Lambda and Fargate, it’s open source and can be used outside of AWS as well.
Unlike Docker, Firecracker doesn’t share the host OS kernel. Each microVM is isolated, secure, and starts in under 125ms. It’s ideal for running multi-tenant workloads, handling untrusted code, or meeting strict security requirements. You get VM-level isolation with container-like speed.
Related read: Best AWS Lambda Alternatives For Serverless Computing
10. Microsoft Azure Container Registry – Managed OCI distribution
With Microsoft Azure Container Registry, you gain access to a private Docker registry that helps you store and manage container images using Docker Command-Line Tools. In addition to offering robust security features, it offers Twist Lock compatibility, runtime protection, and scanning for container vulnerabilities.
Microsoft Azure is also the second most popular cloud computing platform behind Amazon Web Services (AWS), so it makes sense to run container projects here. You can also deploy, run, and scale apps easily with container orchestrators like Docker Swarm and Kubernetes.
Similar to Docker Hub, Azure Container Registry serves as a catalog of container images, enabling users to manage container contents directly. It also offers integrated authentication and facilitates geo-replication, including tag locking and setting up a private virtual network.
11. Dagger – CI/CD engine for portable, containerized pipelines
Dagger is a modern CI/CD engine built by the creators of Docker. It runs every pipeline step inside containers, ensuring consistency across dev, staging, and production.
Unlike traditional CI tools that rely on complex YAML files, Dagger utilizes a declarative language called CUE to define portable and modular workflows. It works across any CI system, such as GitHub Actions or GitLab, and is useful for teams building container-native platforms.
12. Werf – GitOps-friendly container builder for Kubernetes
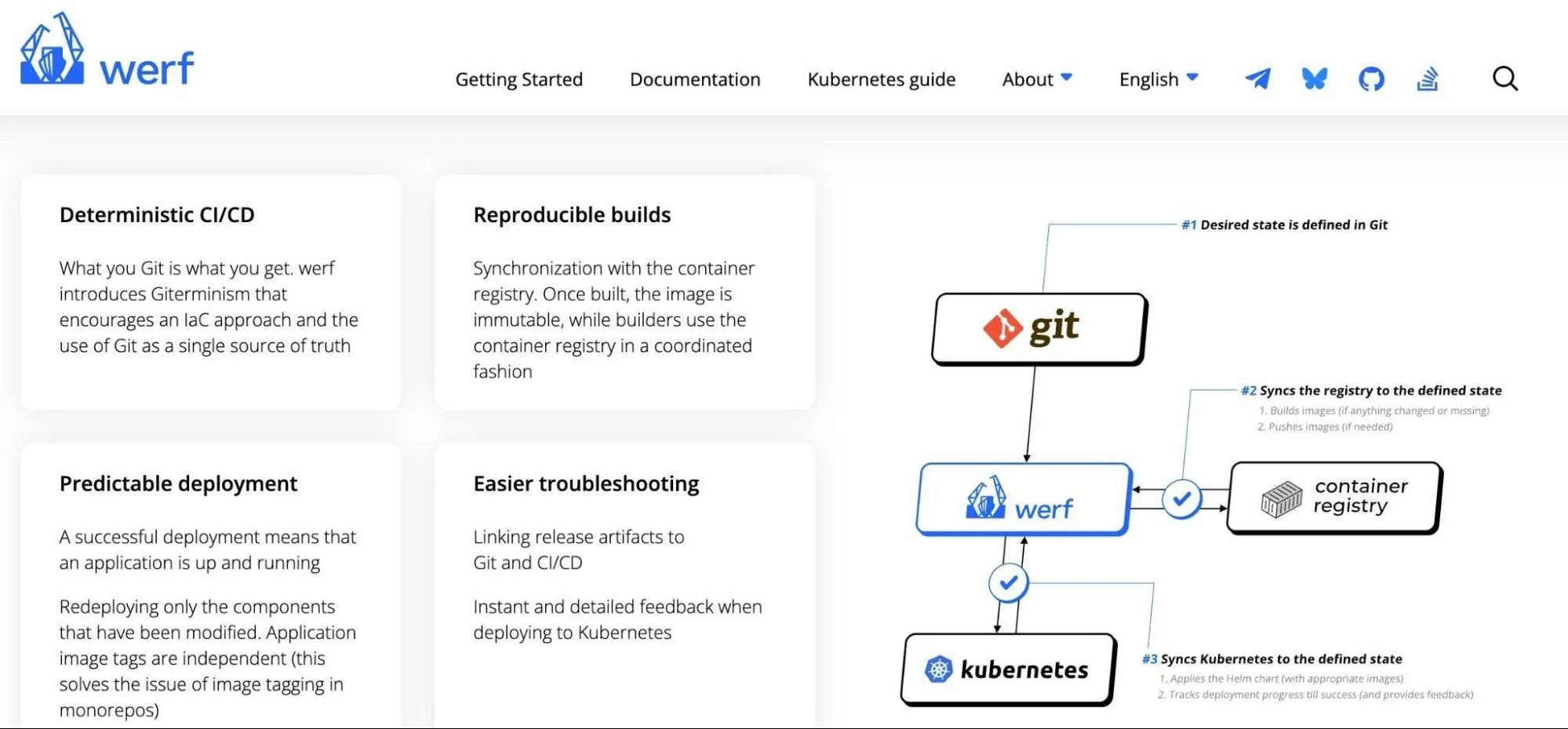
Werf is an open-source tool for building, publishing, and deploying container images in Kubernetes environments.
It builds container images without needing a Docker daemon — perfect for Kubernetes-native environments.
With Werf, you can define and track builds directly from Git commits, making deployments repeatable and auditable. It also integrates with existing tools, such as GitLab CI/CD, GitHub Actions, and ArgoCD.
13. Red Hat OpenShift – Kubernetes-based container platform
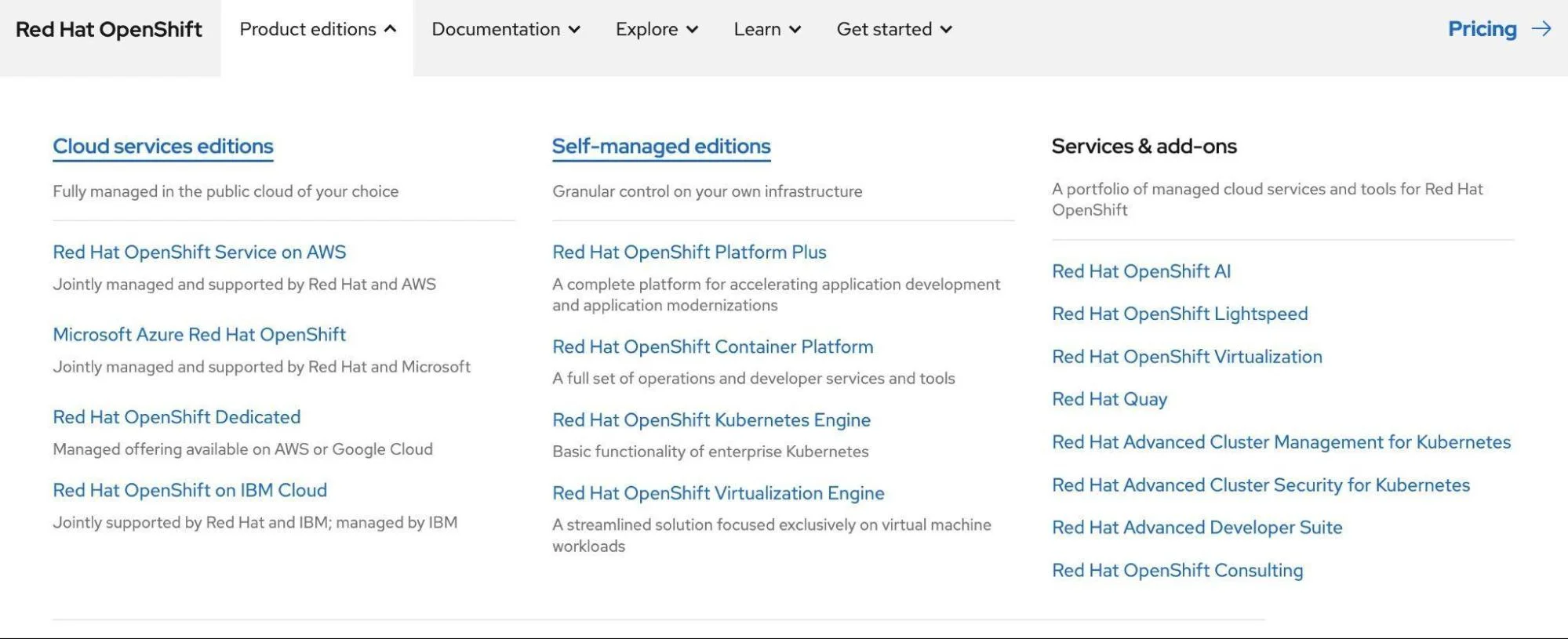
Red Hat OpenShift is a Kubernetes platform that integrates with DevOps tools to improve functionality. It boasts robust features, including automated updates, built-in CI/CD tools, and top-notch security protocols.
OpenShift offers a built-in image registry for storing and sharing Docker images. This enables users to deploy applications directly from their source code repository, adhering to DevOps best practices.
OpenShift also integrates with the rest of Red Hat’s ecosystem. This ensures smooth deployment, management, and scaling of applications in hybrid or multi-cloud environments.
14. Rancher Desktop by SUSE – Kubernetes management tool for desktops
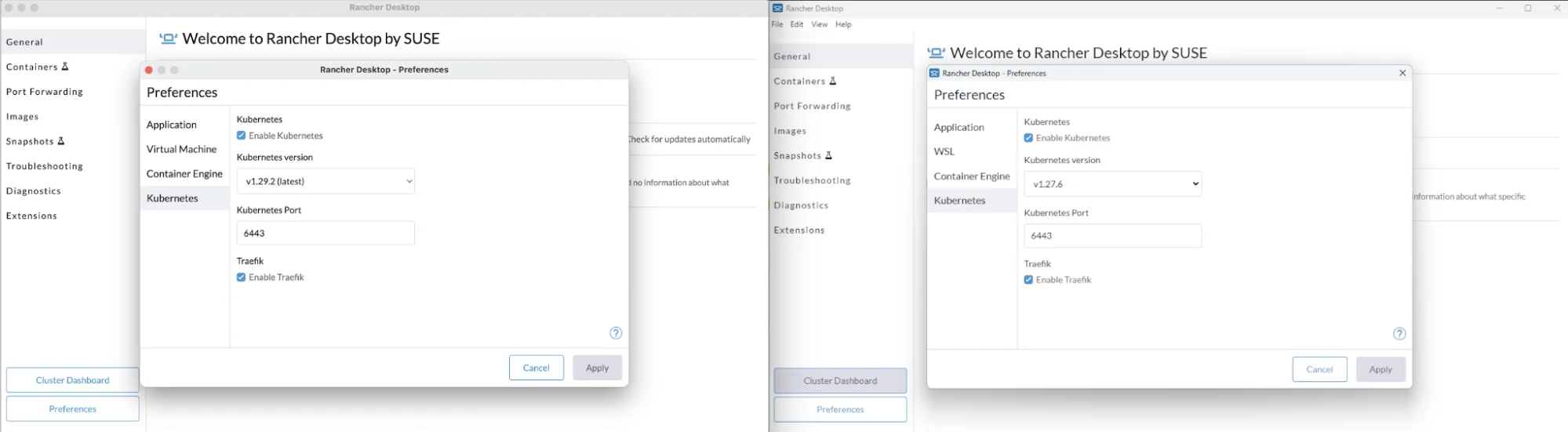
Rancher Desktop is a platform for managing containers that makes it easier to deploy Kubernetes on desktops. It offers an easy-to-use interface and robust features for handling Kubernetes clusters and containerized applications.
Rancher Desktop offers a visual interface that enables developers to build, operate, and manage containers. It provides flexibility in managing containers by supporting both Docker and Containerd runtimes. If you’re evaluating k3s vs k8s for your cluster, Rancher Desktop also ships with k3s by default — making it a good fit for lightweight local Kubernetes development. The platform is ideal for developers who want a simple, Docker-like experience.
15. Apache Mesos – Cluster resource manager
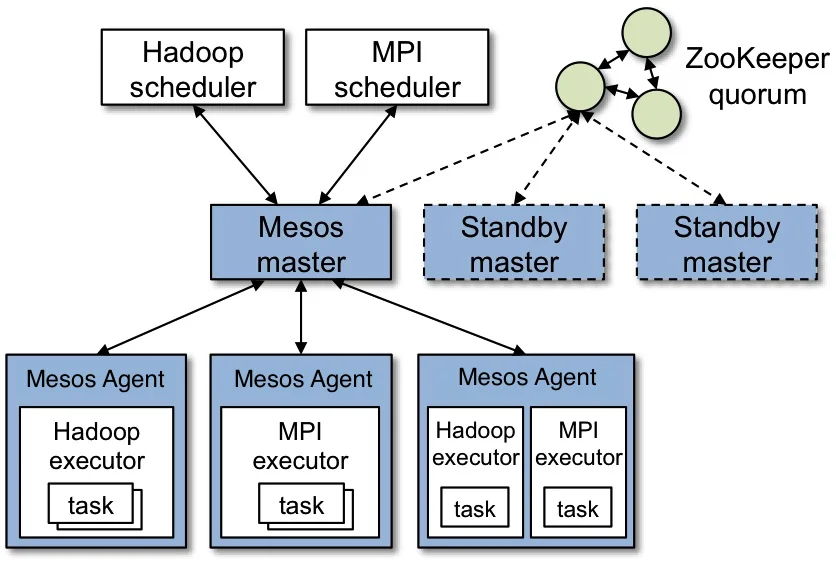
Apache Mesos is a cluster manager that enables effective resource isolation and sharing across distributed applications or frameworks. Its ability to run containerized and non-containerized tasks makes it a flexible option for Docker.
Mesos separates CPU, memory, storage, and other computing resources from individual machines. This allows for fault-tolerant and flexible distributed systems. Its high scalability and capacity to handle extensive clusters make it ideal for demanding, high-performance applications.
16. VirtualBox – Virtualization platform for VMs
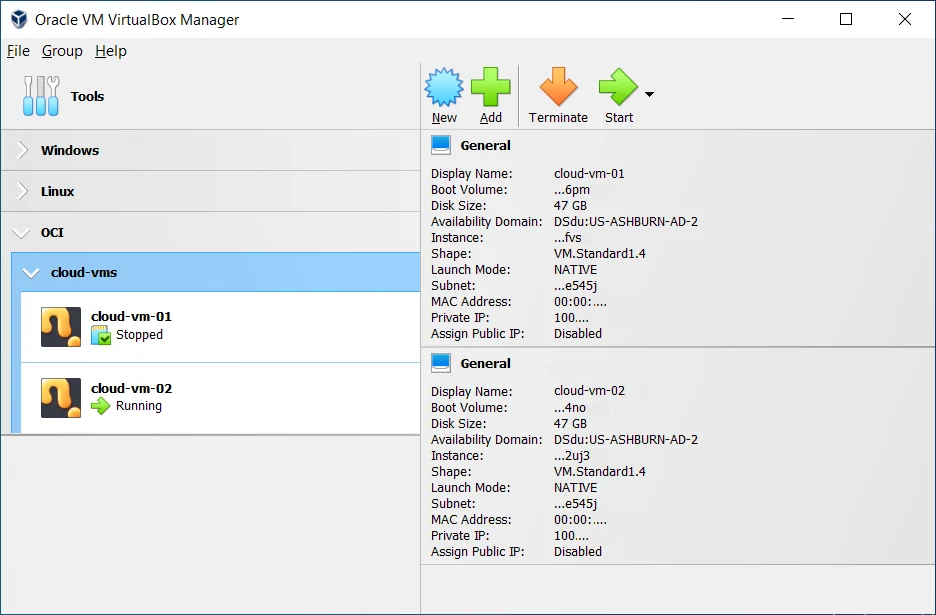
VirtualBox is a virtualization product for x86 and AMD64/Intel64 architectures, suitable for both home and enterprise use. Although not designed specifically for containerization, it provides robust capabilities for running virtual machines.
VirtualBox enables users to create isolated environments for testing and development without disrupting the host system. It is compatible with different operating systems and offers excellent flexibility and ease of use.
VirtualBox offers a reliable option for developers who require a virtualized environment to operate Docker or other container platforms.
But as containers evolve, so do the tools and technology shaping how we build and run them.
2026 Snapshot: What’s Trending In Container Tech?
Here’s what’s driving container innovation:
Serverless and container convergence
Serverless platforms now support OCI-compliant images, making it easier to run containers on serverless infrastructure. Tools such as AWS Fargate, Google Cloud Run, and Azure Container Apps enable teams to deploy containerized apps without managing the backend — or compromising portability.
Related reads:
- A complete guide to serverless computing, how it works, and a few examples
- AWS ECS Vs. EKS Vs. Fargate
eBPF for container observability
eBPF (extended Berkeley Packet Filter) enables teams to trace and monitor containers directly from the Linux kernel — without changing code or installing agents. It’s powering faster, deeper insights into app performance, security, and network traffic, especially in high-scale environments.
WebAssembly (Wasm) for ultra-light workloads
Wasm is now a go-to for edge, IoT, and microservices that don’t need full containers. It spins up fast, runs in isolated environments, and works across platforms. Teams are using it alongside containers to reduce cold start times and resource usage.
What Next: View, Understand, And Control Your Cost Of Containerized And Non-Containerized Apps With CloudZero
You can now choose from a variety of Docker alternatives based on your workload requirements. Yet, whatever tool you add to your stack, using containers shouldn’t come with cost surprises — something that happens all too often.
CloudZero’s cloud cost intelligence platform enables easy collection, analysis, and understanding of costs across both containerized and non-containerized infrastructure — and pairs well with your broader suite of cloud cost management tools. You can view your costs by product, feature, customer, and more, right down to the hour and pod level, regardless of whether you are running entirely on containers or just transitioning.

By combining all your cloud spend into a single platform, CloudZero ensures you never miss a thing.
The result? We empower you with cost intelligence, enabling you to understand the costs associated with running a microservice, supporting a specific customer, deploying and maintaining a given software feature, and more.
Whether your workloads rely on containerized or traditional infrastructure or a combination of both, CloudZero can help.